How to Automate a scheduled power down and on of Azure VMs
How to Automate a scheduled power down and on of Azure VMs
Automate the Shutdown
If you need to create an automated process that shuts down or powers on your Azure VMs to save you from paying fees to Microsoft for services while they are not being utilised, you can do this with the Azure Virtual Machine Scheduler tool that we have created. AVMS as it is known can automate a schedules that you specify to do all this for you and to send you email alerts during the process. You could use AVMS for your Development and Test systems housed within Azure, saving you money while they are not being used.
It is quite a simple process to create a new schedule. Open up the Azure Virtual Machine Scheduling tool and first let it sync with your Microsoft Azure Subscriptions so that it can populate all your VMs.
Start your Azure VM Automation Schedule
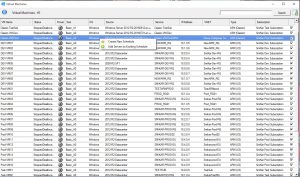
Click the Virtual Machines Icon to show your Azure virtual machines.

List all your Azure VMs
The Azure VM Scheduler / Orchestrator will scan your total Azure Environment and list all your Azure VMs.
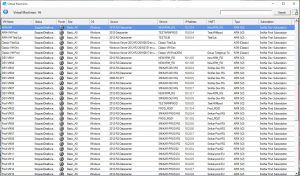
Select your Azure VMs
Select the Azure VMs you want to either power down or power on and make sure that you tick the according checkbox for each machine. Once you have selected all the machines you wish, right click in the console as below and choose create new schedule.
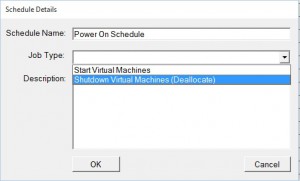
Azure VM Schedule Details
Next, give the schedule a name, use the drop down box to choose whether to automate a power on or shutdown schedule for your Azure Virtual Machines and then a description if you wish to do so. Click OK to continue. In the example below, we can see we are creating a Power on Schedule. Keep in mind, if you wish to power machines on and then off, you will need to go through these steps twice, choosing the appropriate Job type.
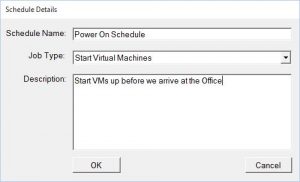
Schedule the Power on of your Azure VMs
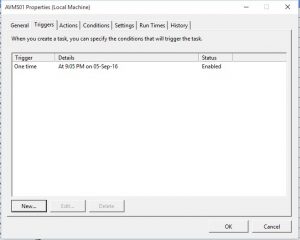
Click NEW to create a new schedule
Choose your Azure VM Power On date and time
Now choose a date and time you wish your Azure virtual machines to Power On. Click OK when ready.
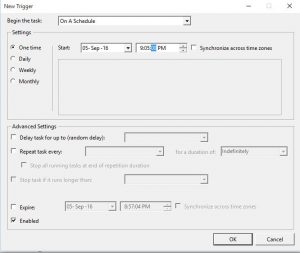
Confirm the Azure VM Power On schedule
Confirm the Date and Time are what you created and then click OK.
Azure VM Power On Schedule Complete
Thats all there is to it. You have now automated a scheduled power down or power on of your virtual machines within Azure.
The Azure Virtual Machine Scheduling tool will now start up your virtual machines with Microsoft’s Azure cloud at the time you specified. If you have setup email alerts, you will be notified when the job starts and completes.

Azure VM Shutdown Schedule
If you now need to complete a Power Off schedule, go through these same steps again, but choose Shutdown Virtual Machines (Deallocate) as show in the window below.
Click this link to learn more about the Azure Virtual Machine Scheduler. Feel free to Download a fully functioning 30 day trial and test it for yourself.
Also, see the other products that SmiKar Software have developed. From SnaPatch our patch management addon for SCCM, SnapShot Master that automates your Vmware or Hyper-V snapshots and even AVMD our free tool that helps deploy Virtual Machines to Microsoft’s Azure cloud.
The Azure Virtual Machine Scheduler tool is an excellent way to automate the power down and on of your Azure VMs, saving you money while they are not being used. It is a straightforward process that can be completed within a matter of minutes. Try it out for yourself and see how it can benefit you. For more information on the Azure Virtual Machine Scheduler and other tools developed by SmiKar Software, click the link provided in this article.