MICROSOFT’S March 2017 PATCH RELEASES
MICROSOFT’S March 2017 PATCH RELEASES
Well after an absence last month of the usual Microsoft Patch Tuesday releases, Microsoft have bundled more in to this months release, with 18 Windows Updates for the month of March 2017.
See how you can remove the risk of patch deployment by adding SnaPatch to your SCCM patching infrastructure?
MS17-006 – Critical
Cumulative Security Update for Internet Explorer (4013073)
This security update resolves vulnerabilities in Internet Explorer. The most severe of the vulnerabilities could allow remote code execution if a user views a specially crafted webpage using Internet Explorer. An attacker who successfully exploited these vulnerabilities could gain the same user rights as the current user. If the current user is logged on with administrative user rights, an attacker who successfully exploited this vulnerability could take control of an affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
MS17-007 – Critical
Cumulative Security Update for Microsoft Edge (4013071)
This security update resolves vulnerabilities in Microsoft Edge. These vulnerabilities could allow remote code execution if a user views a specially crafted webpage using Microsoft Edge. An attacker who successfully exploited these vulnerabilities could take control of an affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
MS17-008 – Critical
Security Update for Windows Hyper-V (4013082)
This security update resolves vulnerabilities in Microsoft Windows. The most severe of the vulnerabilities could allow remote code execution if an authenticated attacker on a guest operating system runs a specially crafted application that causes the Hyper-V host operating system to execute arbitrary code. Customers who have not enabled the Hyper-V role are not affected.
MS17-009 – Critical
Security Update for Microsoft Windows PDF Library (4010319)
This security update resolves a vulnerability in Microsoft Windows. The vulnerability could allow remote code execution if a user views specially crafted PDF content online or opens a specially crafted PDF document.
MS17-010 – Critical
Security Update for Microsoft Windows SMB Server (4013389)
This security update resolves vulnerabilities in Microsoft Windows. The most severe of the vulnerabilities could allow remote code execution if an attacker sends specially crafted messages to a Microsoft Server Message Block 1.0 (SMBv1) server.
MS17-011 – Critical
Security Update for Microsoft Uniscribe (4013076)
This security update resolves vulnerabilities in Windows Uniscribe. The most severe of these vulnerabilities could allow remote code execution if a user visits a specially crafted website or opens a specially crafted document. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
MS17-012 – Critical
Security Update for Microsoft Windows (4013078)
This security update resolves vulnerabilities in Microsoft Windows. The most severe of the vulnerabilities could allow remote code execution if an attacker runs a specially crafted application that connects to an iSNS Server and then issues malicious requests to the server.
MS17-013 – Critical
Security Update for Microsoft Graphics Component (4013075)
This security update resolves vulnerabilities in Microsoft Windows, Microsoft Office, Skype for Business, Microsoft Lync, and Microsoft Silverlight. The most severe of these vulnerabilities could allow remote code execution if a user either visits a specially crafted website or opens a specially crafted document. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
MS17-014 – Important
Security Update for Microsoft Office (4013241)
This security update resolves vulnerabilities in Microsoft Office. The most severe of the vulnerabilities could allow remote code execution if a user opens a specially crafted Microsoft Office file. An attacker who successfully exploited the vulnerabilities could run arbitrary code in the context of the current user. Customers whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights.
MS17-015 – Important
Security Update for Microsoft Exchange Server (4013242)
This security update resolves a vulnerability in Microsoft Exchange Outlook Web Access (OWA). The vulnerability could allow remote code execution in Exchange Server if an attacker sends an email with a specially crafted attachment to a vulnerable Exchange server.
MS17-016 – Important
Security Update for Windows IIS (4013074)
This security update resolves a vulnerability in Microsoft Internet Information Services (IIS). The vulnerability could allow elevation of privilege if a user clicks a specially crafted URL which is hosted by an affected Microsoft IIS server. An attacker who successfully exploited this vulnerability could potentially execute scripts in the user’s browser to obtain information from web sessions.
MS17-017 – Important
Security Update for Windows Kernel (4013081)
This security update resolves vulnerabilities in Microsoft Windows. The vulnerabilities could allow elevation of privilege if an attacker runs a specially crafted application.
MS17-018 – Important
Security Update for Windows Kernel-Mode Drivers (4013083)
This security update resolves vulnerabilities in Microsoft Windows. The vulnerabilities could allow elevation of privilege if an attacker logs on to an affected system and runs a specially crafted application that could exploit the vulnerabilities and take control of an affected system.
MS17-019 – Important
Security Update for Active Directory Federation Services (4010320)
This security update resolves a vulnerability in Active Directory Federation Services (ADFS). The vulnerability could allow information disclosure if an attacker sends a specially crafted request to an ADFS server, allowing the attacker to read sensitive information about the target system.
MS17-020 – Important
Security Update for Windows DVD Maker (3208223)
This security update resolves an information disclosure vulnerability in Windows DVD Maker. The vulnerability could allow an attacker to obtain information to further compromise a target system.
MS17-021 – Important
Security Update for Windows DirectShow (4010318)
This security update resolves a vulnerability in Microsoft Windows. The vulnerability could allow an information disclosure if Windows DirectShow opens specially crafted media content that is hosted on a malicious website. An attacker who successfully exploited the vulnerability could obtain information to further compromise a target system.
MS17-022 – Important
Security Update for Microsoft XML Core Services (4010321)
This security update resolves a vulnerability in Microsoft Windows. The vulnerability could allow information disclosure if a user visits a malicious website. However, in all cases an attacker would have no way to force a user to click a specially crafted link. An attacker would have to convince a user to click the link, typically by way of an enticement in an email or Instant Messenger message.
MS17-023 – Important
Security Update for Adobe Flash Player (4014329)
This security update resolves vulnerabilities in Adobe Flash Player when installed on all supported editions of Windows 8.1, Windows Server 2012, Windows Server 2012 R2, Windows RT 8.1, Windows 10, and Windows Server 2016.
Now that you have made it this far, a quick shameless plug for our software portfolio. 🙂
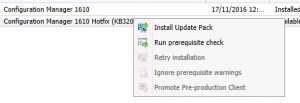
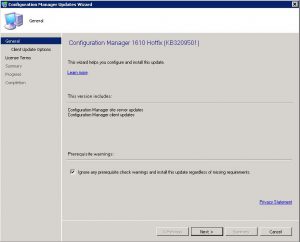
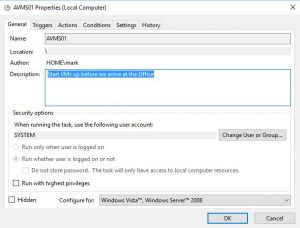
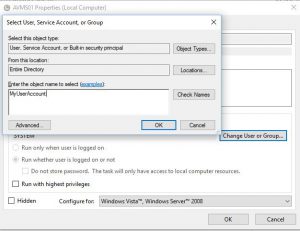
SnaPatch – Patch Management Addon for Microsoft’s SCCM.
SnapShot Master – Take control of your virtual machine snapshots, works with both Hyper-V and Vmware.
Azure Virtual Machine Cloner – Quickly and easily clone your Azure VMs, you can even migrate your VMs between ARM and ASM.
Azure Virtual Machine Scheduler – Save money and schedule the shutdown and power on of your virtual machines within Microsoft’s Azure Cloud.
Azure Virtual Machine Deployer – Deploy VMs to Microsoft’s Azure cloud easily, without the need for powershell.