by Mark | Jul 5, 2016 | Deployment, How To, Patch Management, Patch Releases, Risk, SCCM, Security
Deploying a Zero Day Exploit Fix with Microsoft SCCM 2012
Zero Day exploits are vulnerabilities that are found and can be used by hackers to exploit and use for malicious or personal intent. These exploits have been known to affect both software and hardware, causing issues to programs, data, computers, and networks. Once a patch or fix is released by the vendor, the issue is no longer known as a Zero Day vulnerability. In this article, we will discuss how to remediate Zero Day attacks and how to deploy a Zero Day exploit fix using Microsoft SCCM
Remediating Zero Day Attacks
Unfortunately, there isn’t much that can be done until a fix or update is released that patches the security hole. Once a patch is released, it is best to deploy and apply the patch as soon as possible. To reduce the risk of unknown vulnerabilities, it is good practice to keep your hardware and software up to date. This will remove any previously found vulnerabilities from your environment as patches are applied. Having a patching process in place and suitable infrastructure to do so (e.g., Microsoft SCCM and SnaPatch) where you can deploy updates easily and often are also good practices.
Deploying a Zero Day Exploit Patch Using SCCM
Unfortunately, there isn’t much that can be done until a fix or update is released that patches the security hole. Once a patch is released, it is best to deploy and apply the patch as soon as possible. To reduce the risk of unknown vulnerabilities, it is good practice to keep your hardware and software up to date. This will remove any previously found vulnerabilities from your environment as patches are applied. Having a patching process in place and suitable infrastructure to do so (e.g., Microsoft SCCM and SnaPatch) where you can deploy updates easily and often are also good practices.
Zero Day Exploit Overview
So what exactly is a Zero Day Exploit you ask? To be exact, a Zero Day Exploit is a vulnerability that is found that a possible Hacker can use to exploit and use for malicious or personal intent. The Vendor (software or hardware) has Zero Days to plan, mitigate and fix the issue so that there is no further exploitation of the vulnerability. The exploits have been known to be for either software (Operating Systems and Software) and hardware. They have been known to cause issues to programs, data, computers and to the network.

Zero Day Attack Timeline
In the case of a breach being found in some software, a Zero Day Exploit normally follows this;
- A hacker finds a vulnerability with a product (software/hardware).
- The hacker writes an exploit and uses it either to be malicious or financial gain.
- Exploit is detected either by Users, Security Companies or the Vendor themselves.
- The Vendor studies the new exploit and develops a fix.
- The Vendor releases a new patch to fix the exploit
- Users install the Patch or Virus Definition update.
The biggest issue with a Zero Day Exploit is that they are generally unknown until they have been used to breach systems, leaving everyone vulnerable until the Vendor releases security advice on how to remediate the issue or a patch or update. This could be days, weeks, months or even years before the Vendor learns of the vulnerability. Once a Patch or Fix has been released by the Vendor, then the issue is no longer known as a Zero Day Vulnerability.
How to remediate Zero Day Attacks
Unfortunately there isnt much that can be done until there is a fix or update released that patches the security hole. Once a patch is released it is best to deploy and apply the patch as soon as is possible.
To also reduce the risk, it is good practice which will aid you in mitigation of vulnerabilities that are unknown to yourself if you keep your hardware and software patched up to date. This will remove from your environment any previously found vulnerabilities as patches are applied. Having a Patching Process in place and suitable infrastructure to do so (ie Microsoft SCCM and SnaPatch for instance) where you can deploy updates easily and often are also good practice.
Using SCCM to deploy a Zero Day Exploit Patch
If you are using Microsofts SCCM 2012, you can easily deploy an update that addresses a Zero Day Vulnerability by following these steps;
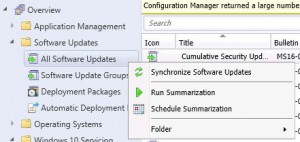
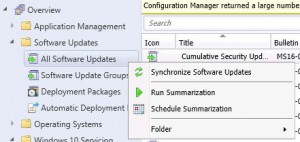
- Log on to your SCCM console, then go to Software Library, then expand Software Updates and highlight All Software Upates. Now Right Click and choose Synchronise Software Updates. This will synchronise your SCCM server with your WSUS updates server. Allow a few minutes for the new updates to populate the view. You can check the Wsyncmgr.log to view the update synchronisation.
- If you know the Bulletin ID number (the update number released by Microsoft in the format MSXX-XXX. In this example I am choosing MS16-082), you can now search for this within the console.

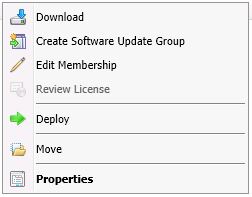
- Make sure that the update has downloaded and if not, right click the update and choose Download. You will obviously need to give the update sometime to download in to your environment and be ready for deployment. Click this link to see how to manually download updates if you dont know how.
- When the update is downloaded and ready for deployment, you are now ready to deploy the Update. (If you are using SnaPatch to deploy the updates, go straight to the SnaPatch Section below.)
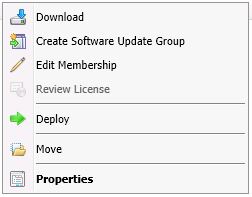
Right Click the update (or updates) and choose Deploy.
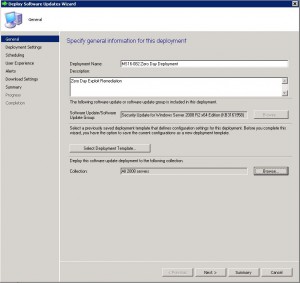
Enter in a Deployment Name, a Description, and choose the collection you wish the Zero Day exploit to deploy to. Once you have chosen the correct settings, click on Next.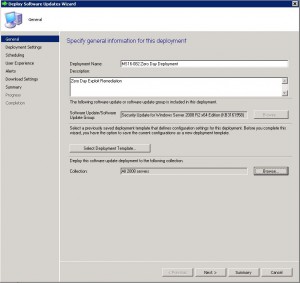
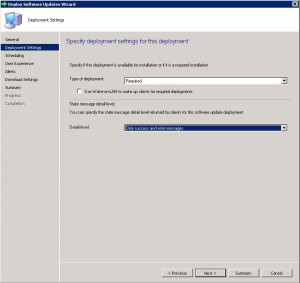
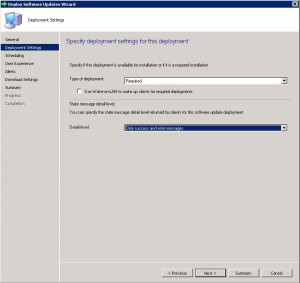
- On the Deployment Tab, leave the type of deployment as Required and choose the level of detail you want then click on Next.
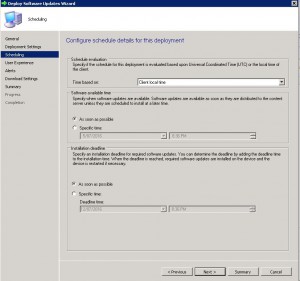
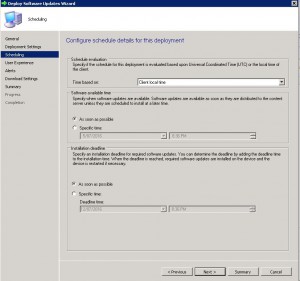
- Now to schedule when you want the update to deploy. As this is a Zero Day Exploit that you want patched quickly, schedule the patch to be available As Soon As Possible for both the Software Available Time and Installation Deadline. Please note, that more often than not, the installation of an update will cause systems to restart. Please make sure you have informed the appropriate people and that you have approval for deployment. Nothing worse than deploying an update and having to answer to Management as you caused unwarranted system outages.
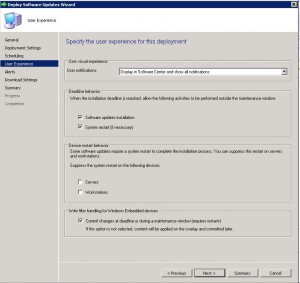
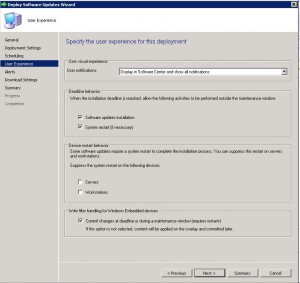
- The User Experience Tab is where you set how the deployment will interact with Users. You can set if the users are notified within the Software Centre that an update is available for installation, when the deployment deadline is reached whether the update can install and restart the system outside a maintenance window, and finally whether you wish to suppress a system restart. As this is an urgent deployment, I have chosen to allow installation and restart to be allowed outside any maintenance windows. Choose the settings you require and click on Next.
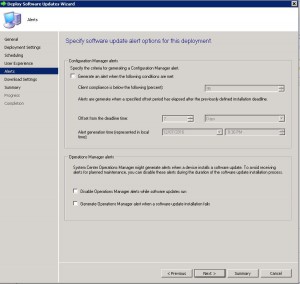
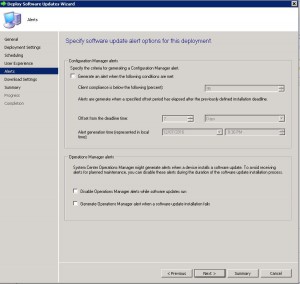
- If you have System Centre Operations Manager (Microsoft SCOM) in your environment you can choose to generate an alert with criteria you specify. In this example we are not going to specify any settings. Click on Next when you have made your selections.
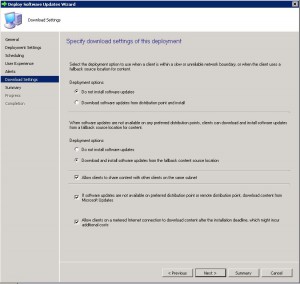
- The Download Settings tab allows you to choose client download settings. If a client is on a slow or unreliable network boundary you can choose if they dont install the update or from another distribution point. Allowing clients to share content between themselves is a great feature of SCCM as it will stop other client machines downloading the same updates and possibly flooding a network link. The clients will all share the update between themselves if they are on the same subnet. Also if they cannot download the update from a SCCM distribution point, allowing them to download from Microsoft Update is available as well.
Click on Next when ready to.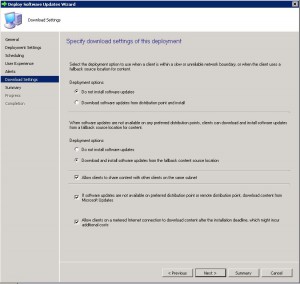
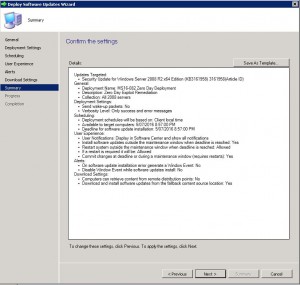
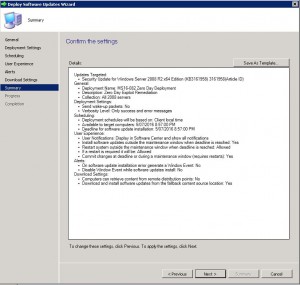
- Now you can review all the settings on the Summary Tab. Confirm you are happy with all the settings and then click Next.
- The progress of the deployment will now be shown.
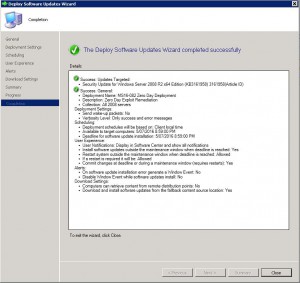
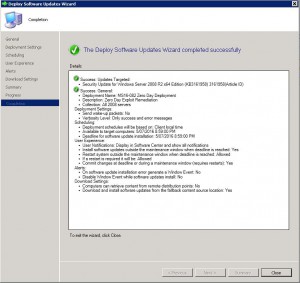
- Your Zero Day Exploit deployment should now be ready to be deployed to your SCCM clients as per the settings you have set.
Using SnaPatch for Zero Day Exploit Deployment
If you are using SnaPatch to aid you with the deployment of Windows Updates with Microsoft’s SCCM, you can follow on from Steps 1 to 4 from above.
- Open the SnaPatch console and choose the SnaPatch Icon to start the snapshot and patch deployment process.

- Now you are presented with all the SCCM Collections and Systems available to deploy the Zero Day Exploit to. Choose the systems you want to receive the patch and click on Add.

If the machines are virtual (either a VMWare or HyperV virtual machine) you can choose whether to take a snapshot of the servers prior to deployment of the zero day patch. Should the servers not have a successfully snapshot completed, then they will not receive the update deployment. The snapshot of the virtual machines gives you a quick rollback position should the update cause an issue in your environment.
When you have chosen all the machines you wish and if you would like a snapshot, click on the green arrow to continue.
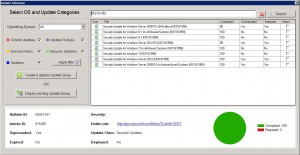
- The next window in the SnaPatch process, is to chose the update you wish to deploy. As this is a Zero Day patch and we know the Microsoft article number (which in this example is MS16-082), type in the KB or MS article number and choose search.
Select the update, confirm that it has been downloaded (as per step 3 above) and now choose if you want the update to deploy to an existing Update Group or to create a new one. 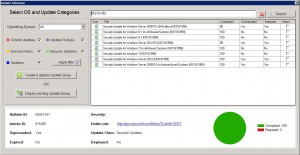
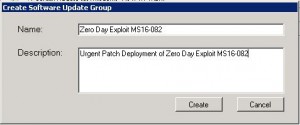
- As this is an urgent deployment, I am choosing Create & Deploy Update Group. Give the Software Update Group a Name and Description and click Create.
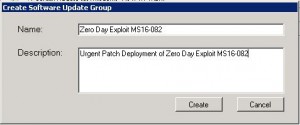
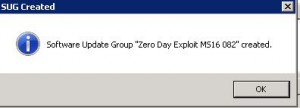
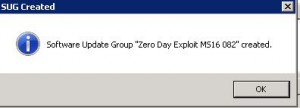
- Confirmation that the Software Update Group has been created. Click OK.
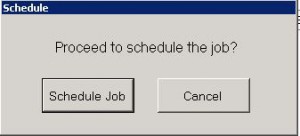
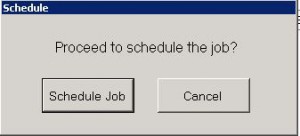
- Next we have to schedule deployment. Click Schedule Job.
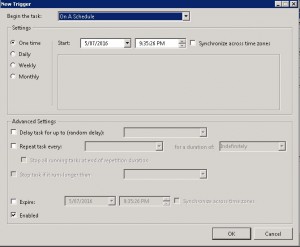
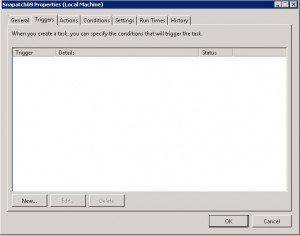
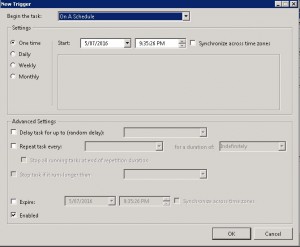
- Now on the scheduling window, click on New.
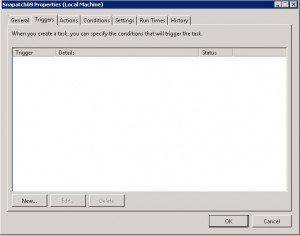
- Choose an appropriate schedule when you would like the deployment to happen. This will set up the update deployment for the time you specify. Click OK when you are ready to proceed, then close the scheduling Window.
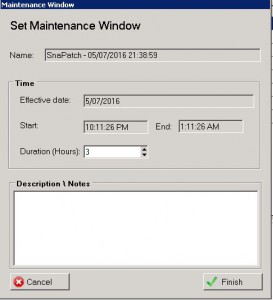
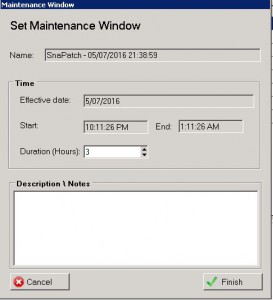
- On the Maintenance Window choose the duration you want the snapshots to be performed and the updates to be installed during. Click on Finish when complete.
 Thats all there is to it. SnaPatch will now create a deployment of the Zero Day Exploit Patch within Microsoft SCCM and set the Maintenance Window. When the maintenance window is reached, SnaPatch will interact with your Vmware or HyperV hosts and start a snapshot of the servers you have selected. Once the snapshot is complete SnaPatch then contacts SCCM and allows SCCM to deploy the patch to those servers. You will also receive email notifications throughout the snapshot and deployment process.
Thats all there is to it. SnaPatch will now create a deployment of the Zero Day Exploit Patch within Microsoft SCCM and set the Maintenance Window. When the maintenance window is reached, SnaPatch will interact with your Vmware or HyperV hosts and start a snapshot of the servers you have selected. Once the snapshot is complete SnaPatch then contacts SCCM and allows SCCM to deploy the patch to those servers. You will also receive email notifications throughout the snapshot and deployment process.
Click for further information on SnaPatch Patch Management.
Zero Day exploits can cause serious issues to programs, data, computers, and networks. It is essential to deploy patches and fixes as soon as possible to reduce the risk of exploitation. Using Microsoft SCCM 2012 to deploy a Zero Day exploit fix is an easy process that can be completed by following the steps outlined above. Keeping your hardware and software up to date and having a patching process in place are good practices to mitigate the risk of unknown vulnerabilities.
by Mark | Jun 28, 2016 | Deployment, How To, Patch Management, SCCM
SCCM Automatic Deployment Rule
As a system administrator, managing updates for your organization’s desktops, laptops, and servers can be a challenging task. It requires a lot of time and effort to keep your machines up-to-date with the latest software updates and security patches. However, with the SCCM Automatic Deployment Rule (ADR) feature, you can automate the entire update management process and save valuable time.
An Automatic Deployment Rule (ADR) is a useful feature for organizations using System Center Configuration Manager (SCCM) to manage their IT environment. With an ADR, administrators can automate the process of downloading, approving, and deploying software updates to client machines, saving time and effort compared to manually managing updates. Additionally, an ADR ensures that machines are up-to-date with the latest software updates and security patches, reducing the risk of security vulnerabilities and software bugs. By creating an ADR, administrators can specify what products and severity of updates they want to download, approve, and deploy, giving them greater control over the update management process. Overall, an ADR is an effective tool for streamlining the software update management process and maintaining a secure and up-to-date IT environment.
In this article, we’ll explore the SCCM Automatic Deployment Rule feature and show you how to create an ADR for your organization’s update management.
SCCM Automatic Deployment Rule FAQs
What is an ADR in SCCM?
An ADR is a feature of SCCM that automates the process of downloading, approving, and deploying updates to client machines.
How does an ADR work?
An ADR downloads the latest updates as per the requirements set by the administrator, distributes them to distribution points, and then deploys them to the target collection during the maintenance and deployment windows specified.
What are the benefits of using an ADR in SCCM?
The benefits of using an ADR include automating the update management process, saving time and effort for system administrators, ensuring machines are up-to-date with the latest software updates and security patches, and enabling control over what products and severity of updates to download, approve, and deploy.
How do I create an ADR in SCCM?
To create an ADR in SCCM, you need to open the SCCM console, navigate to the Software Library, expand Software Updates, and select Automatic Deployment Rules. From there, you can follow the steps to create an ADR, including selecting the products and classifications to include, configuring the deployment settings, and specifying the collection to which the updates will be deployed.
What are some best practices for using an ADR in SCCM?
Best practices for using an ADR in SCCM include following guidelines for patch management, creating a patch management process, setting maintenance and deployment windows, and monitoring Microsoft’s monthly patch releases.
Can an ADR be scheduled to run at a specific time?
Yes, an ADR can be scheduled to run at a specific time, such as after Microsoft’s monthly patch release.
How to create a SCCM Automatic Deployment Rule
ADR Creation
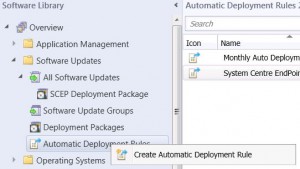
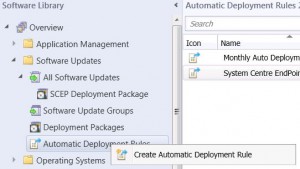
Creating the ADR is fairly easy process. Open your SCCM console and navigate to SOFTWARE LIBRARY, then expand SOFTWARE UPDATES. Now right click AUTOMATIC DEPLOYMENT RULES and choose CREATE AUTOMATIC DEPLOYMENT RULE.
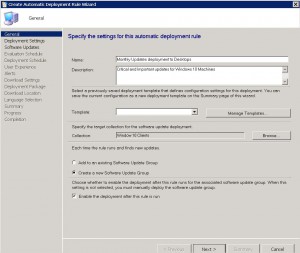
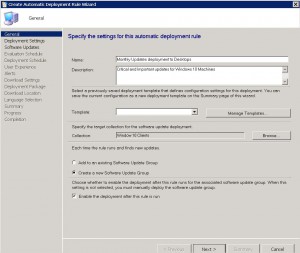
ADR General TAB
Now give the rule a descriptive NAME that will easily identify what this ADR is for (ie Monthly Update deployment to Desktops), a DESCRIPTION, choose a TEMPLATE (I choose Patch Tuesday) and then the TARGET COLLECTION. Now you will need to choose between CREATE A NEW SOFTWARE UPDATE GROUP or to ADD TO AN EXISTING SOFTWARE UPDATE GROUP. The differences between these two settings is, Add to an existing Software Update Group will create a new Software Update group the first time it runs, but then subsequent schedules of the ADR will utilise this update group, or creating a new software update group will create a new update group each time the ADR runs. Choose one of the options and then click on NEXT.
(Make sure you have the checkbox enabled, ENABLE THE DEPLOYMENT AFTER THIS RULE TO RUN).
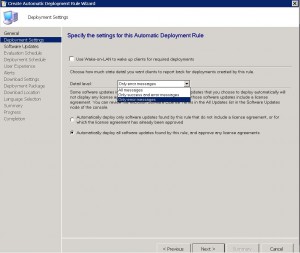
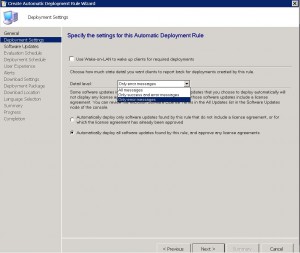
ADR Deployment Settings TAB
We are now presented with the Deployment Settings page next. You can choose to use Wake On Lan (if you have that enabled in your environment) and what level of detail we want regarding the Patch Deployment. You can also specify to Automatically deploy all software updates found by this rule and approve any license agreements. Obviously this will automatically approve and licenses agreements that may be required to deploy the updates, a very handy feature. Once you are happy to proceed, click on NEXT.
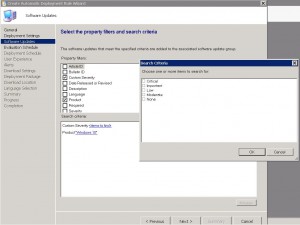
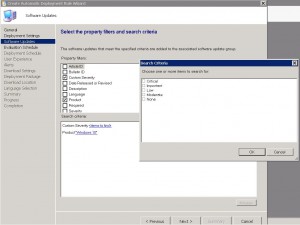
ADR Software Updates TAB
Next we get to choose the products and the severity among other things for the ADR. Choose the products you want (ie in this example Im choosing Windows 10) and the patch severity (Critical, Important, Low, Moderate or None) and date the patches were released (following on from my previous comments, I want the last months patch releases) . Click on NEXT when you have chosen the products you wish patches deploy to.
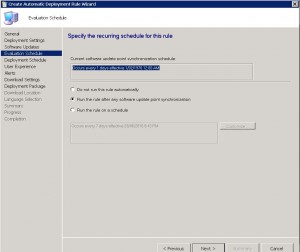
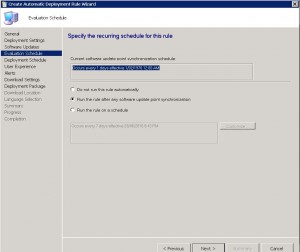
ADR Evaluation Schedule TAB
This tab allows you to configure the settings for when you would like the SCCM Automatic Deployment Rule to evaluate available software updates. You need to configure this schedule to run less frequently than your SUP synchronisation will run (highlighted in the example picture below). You can choose not to run this rule automatically (ie you will have to run this manually if required), after the SUP synchronisation happens (which is the default) or according to a schedule you specify.
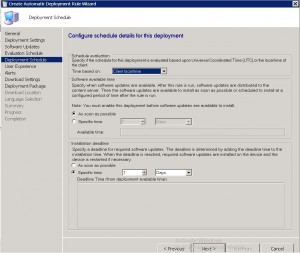
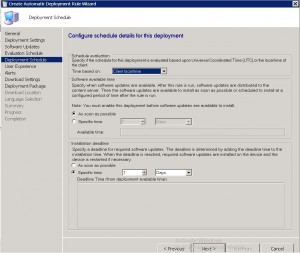
ADR Deployment Schedule TAB
On the ADR deployment schedule TAB, we choose when we would like our updates to be deployed to our client machines. You can choose Universal Coordinated Time or Client machine local time, when you would like the updates to be available to clients, and the software installation deadline. Choose the last two settings carefully as the wrong choice will have a major impact on your environment and users if incorrect.
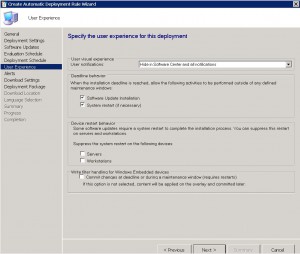
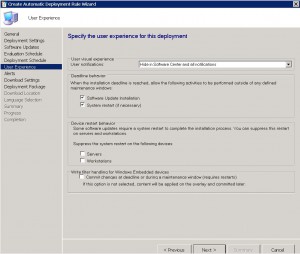
ADR User Experience TAB
One of the most important TABS, is the User Experience TAB. Do you wish to notify the users that updates are available and have them install them prior to the deadline you have set? Would you like the machines to automatically install restart at the deadline? Do you want to suppress a restart on Desktops or Servers, or even both? Choose the required settings and then click NEXT.
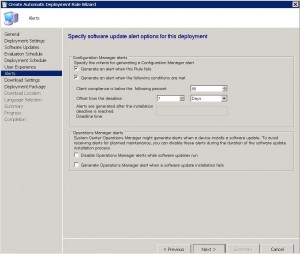
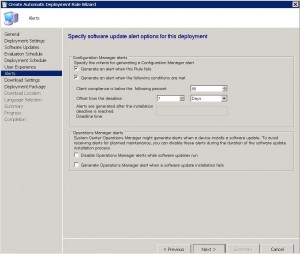
ADR Alerts TAB
The SCCM Automatic Deployment Rule alerts TAB is next. Various settings are available of how you would like to be alerted. From when the rule fails, to compliance settings to alert you of the percentage of machines that are compliant. Additionally, you can generate alerts to System Centre Operations Manager (or SCOM) if you have this in your environment. Again, choose your required settings and click on NEXT.
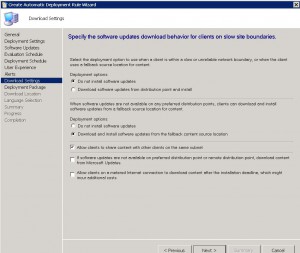
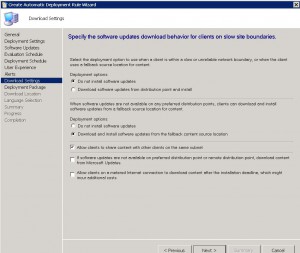
ADR Download Settings TAB
The ADR download settings tab will allow you to specify what and where the client machine downloads the updates from. Obviously, if they are connected to your corporate LAN, the nearest SCCM distribution point is the ideal location. Should the updates not be available on a preferred distribution point, then you can choose not to install updates, or from a fallback location. Allowing the client machines to share the update content with other clients on the same subnet is a great thing to have, especially if they do not have a local SCCM distribution point, or are on a slow WAN link. Additionally, you can allow those clients to download from Microsoft Update.
Click on NEXT when ready to proceed.
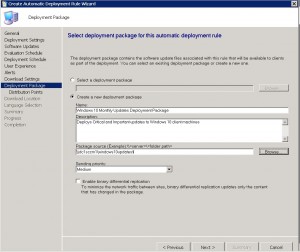
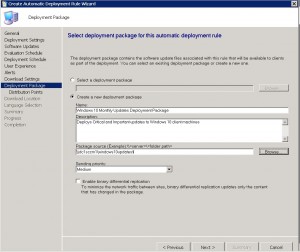
ADR Deployment Package TAB
We can now create a new deployment package, or select an existing one. I will create a new deployment package in this example to show you how that is done.
Choose CREATE A NEW DEPLOYMENT PACKAGE.
Give the deployment package a descriptive name, a description that is easy to identify, where you would like the source files to live (remember this should be a UNC path, so make sure to have shared out the folder and given the correct permissions for SCCM to save the updates to).
Click on NEXT when completed.
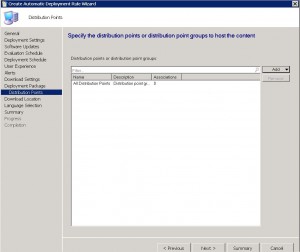
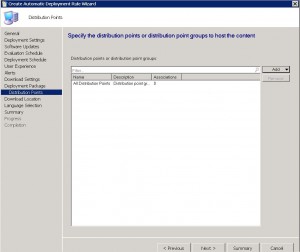
ADR Distribution Points TAB
Select the distribution points you wish the updates to be available from and for you client machines to download from. You can choose individual SCCM Distribution Points, or a Distribution Point Group. Click on NEXT when you have entered these details.
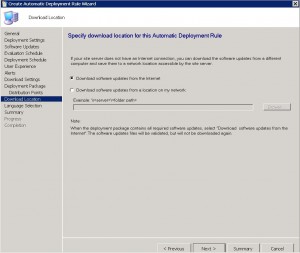
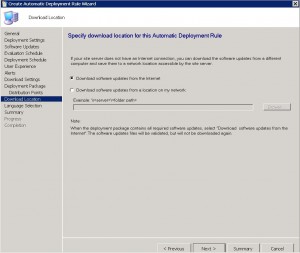
ADR Download Location TAB
Choose where to download the updates from. Should you have a location where updates are downloaded, you can specify that, or should you be using a Microsoft’s WSUS Server, to download them directly from the internet. Click on NEXT when done.
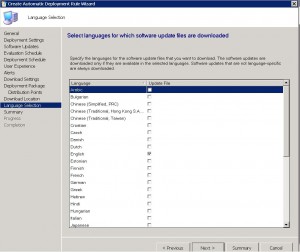
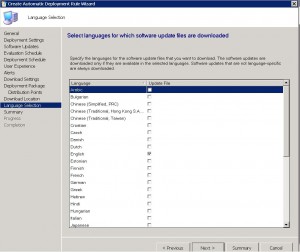
ADR Language Selection TAB
Now choose the appropriate languages you want the patches to download in and then click NEXT.
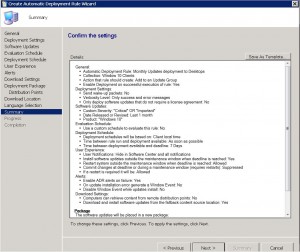
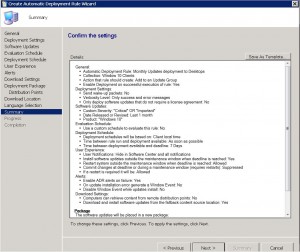
ADR Summary TAB
We are almost there. Almost finished. At the SCCM Automatic Deployment Rule Summary TAB, review the choices you have made and make sure they are correct. When you are happy with the settings, click on NEXT to continue.
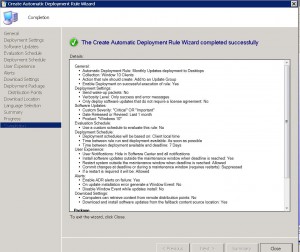
ADR Completion TAB
We made it. We finally got there. The Automatic Deployment Rule is now setup and will run with the settings you have specified. You can now close the wizard.
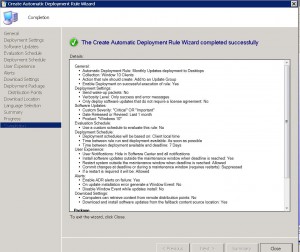
If you followed this post and were careful with the settings you have chosen for your SCCM Automatic Deployment Rule, then the updates you have selected will now deploy to your client machines, when and how you have requested.
See how SnaPatch can help you with Patching your Virtual Server environment.

by Mark | Jun 22, 2016 | How To, Patch Management, SCCM
Creating an Effective Patch Management Process for Your Enterprise
As cyber threats continue to grow in number and complexity, keeping your enterprise’s software and hardware up-to-date is crucial for maintaining security. A robust patch management process is key to achieving this goal. In this article, we’ll explore the steps involved in creating an effective patch management process that will help you reduce risk, save time and effort, and gain auditor approval.
Overview of Patch Management Process
One of the critical tasks for administrators is to create a patch management process that can deploy and manage software updates. Admins need to keep track of multiple sources, including blogs, emails, RSS feeds, and forums, to stay up-to-date with the latest vulnerabilities and patches. Having an outdated system can lead to vulnerabilities and potential security holes that hackers can exploit. In large enterprises that require compliance with ISO 27001, ISO 270012, or even SOX (Sarbanes-Oxley), outdated applications, hardware, and systems can raise red flags during audits.
To create a patch management process, you need to follow a set of procedures that involve various stages, including patch management risk, patch management software, and patch deployment.
Patch Management Software
One of the best patch management software available for managing a server and desktop fleet is Microsoft’s System Centre Configuration Manager (SCCM). SCCM not only automates the download and deployment of updates but also inventories all your systems and software, making life easier for administrators responsible for large environments. SCCM should have an up-to-date inventory of your environment, including the operating system types, to deploy patches to the right machines.
Patch Deployment
Automating the deployment of updates to your machines using an Automatic Deployment Rule within SCCM can save time and effort. Setting this rule to coincide when Microsoft releases its monthly updates (Patch Tuesday) is good practice. Before deployment, it is crucial to test the update to ensure it doesn’t break any systems. Gaining approval for deployment will require some sort of rollback functionality.
.
The Patch Management Process for deployment of updates follows these steps:
- SCCM downloads the latest updates from Microsoft on Patch Tuesday.
- Administrator socializes the latest patch releases with relevant parties.
- CAB (Change Approval Board) approval is required for deployment of the latest patches to the Pilot Group.
- The administrator sets a maintenance window and schedules when the patches should be installed.
- Patches are deployed to the Pilot group.
- UAT (User Acceptance Testing) is performed to ensure no issues arise due to patch deployment.
- Once UAT approval has been gained, the administrator presents a new Change Request to CAB for approval of the deployment of patches to Production systems.
- Approval has been accepted, and the administrator sets up a new deployment package for deployment to Production systems.
Patching Risk
Not having Pilot or Development and Test systems that mirror Production can create a roll-back position that is required before CAB will approve any update deployment. This often means the administrator spends late nights ensuring backups are successful or creating snapshots before allowing updates to deploy.
SnaPatch – SCCM Patch Management Addon Software – Reduce Effort and Risk

SnaPatch is an add-on software for Microsoft’s System Centre Configuration Manager that interfaces with your existing SCCM and virtual environment. SnaPatch will automate a snapshot of your virtual servers before SCCM deploys monthly updates, allowing you to gain the auditors’ approval for your ISO 27001, ISO 270012 or even SOX (Sarbanes-Oxley) patching compliance. This process that SnaPatch completes automatically, will give you a quick roll back position should a patch cause errors to your virtual servers. SnaPatch automates it all, from downloading the latest monthly Windows Updates, to completing a snapshot of your servers prior to patches being deployed, then communicating with SCCM that the patches can now deploy, and finally deleting the snapshot after a period of time, all while emailing you alerts about your patching progress.
In conclusion, creating and maintaining a well-defined patch management process is critical for ensuring the security of your environment. Automated patch deployment and testing are essential to save time and reduce effort, while add-on software like SnaPatch can help reduce risk and gain auditor approval. It’s important to understand the risks associated with outdated systems and the potential harm that can occur if those vulnerabilities are exploited. Don’t wait until it’s too late; start developing your patch management process today to keep your enterprise safe and secure. By following the guidelines outlined in this article, you can reduce risk, save time and effort, and ensure compliance with industry standards.

by Mark | Jun 19, 2016 | How To, SCCM
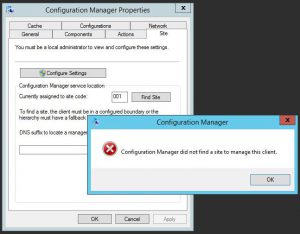
How to Resolve “Configuration Manager Did Not Find a Site to Manage This Client” Error
If you’re an IT professional, you may have encountered an error message that says “Configuration Manager did not find a site to manage this client” when trying to deploy Windows updates to your client machines. This error can be frustrating, especially when you’re not sure what’s causing it. In this article, we’ll discuss how to troubleshoot and fix this error.
Checking the SCCM Client Site
The first step in troubleshooting this error is to check the Configuration Manager applet on each of the affected clients to see if they belong to a client site. If they don’t, this could be the root cause of the error.
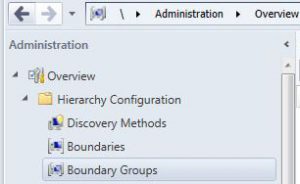
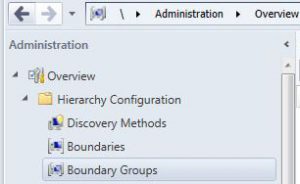
Checking the SCCM Boundary Groups
One possible reason why the clients don’t belong to a site is that there is an issue with the boundary groups. To check if this is the case, go to Administration, Hierarchy Configuration, then Boundary Groups on the Configuration Manager server. If you don’t see any boundary group set up, then you need to create one.
Creating a Boundary Group in SCCM
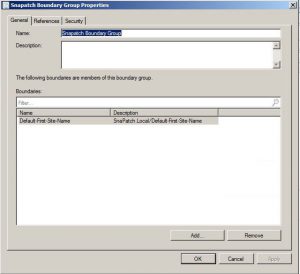
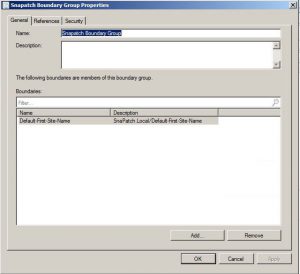
To create a boundary group, right-click on the blank area of the console and choose Create Boundary Group. You’ll then need to fill in the details of your boundaries and assign them the corresponding distribution point and site code. Give the boundary group a name and assign the appropriate boundary.
Assigning Site System Server and Choosing the Assigned Site
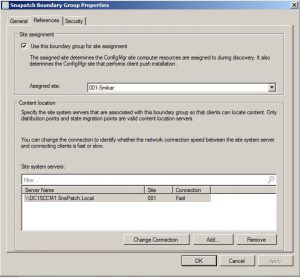
Once you’ve set up the boundary group, go to the References tab and assign the correct Site System Server for this boundary. Choose the assigned site and repeat these steps for each boundary and distribution point that you require.
Site Discovery
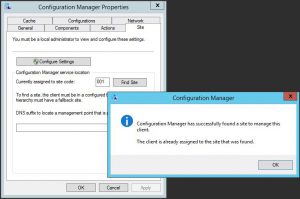
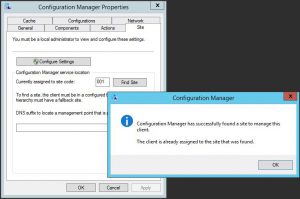
After setting up the boundary group, go back to your client machines and try another site discovery.
So how did we fix this SCCM Error?
In our Lab we had an issue where during Windows Update deployments as it seemed some clients were not getting their updates. Looking through various logs, we eventually checked the Configuration Manager applet on each of the clients and found they didnt belong to a client site.
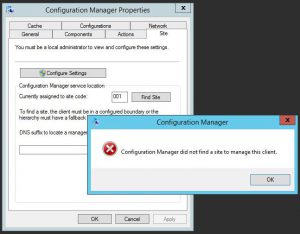
First thing that came to mind, was that there is an issue with a boundary. As this was a recently new implementation of SCCM 2012 in the lab, I logged on to the Configuration Manager server, and opened the SCCM Console.
Go to Administration, Hierarchy Configuration, then Boundary Groups.
Looking at the Boundary Groups, there was never one setup. A slight mistake if we must say! 🙂
To set up a Boundary Group, right click in the blank area of the console and choose Create Boundary Group
From here, you will need to fill in the appropriate details of your Boundaries, and assign them the correlating distribution point and site code.
Give the Boundary Group a Name, and assign the appropriate Boundary.
Go to the References tab.
Now assign the correct Site System Server for this boundary and choose the Assigned Site.
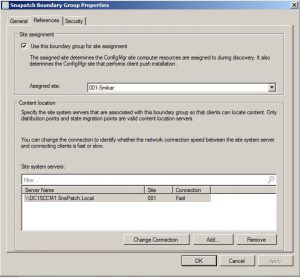
Repeat theses steps for each boundary and DP that you require.
You should now be able to go back to your client machines, and try another site discovery. If all is well you should get the following prompt.
Manually download updates with SCCM
The “Configuration Manager did not find a site to manage this client” error can be caused by several factors, but a missing or improperly configured boundary group is often the culprit. By following the steps above, you should be able to resolve this error and successfully deploy updates to your client machines. Remember to regularly check the Configuration Manager applet and the boundary groups to ensure that everything is functioning as expected.

by Mark | Jun 19, 2016 | How To, Patch Management, SCCM
Microsoft SCCM update deployment best practices
Microsoft SCCM (System Center Configuration Manager) is a powerful tool for deploying updates to Windows-based computers. However, deploying updates with SCCM can be tricky if you don’t follow best practices. In this article, we will discuss some of the best practices that Microsoft recommends for deploying Microsoft Updates from SCCM 2012.
Limit Software Updates to 1000 in a Single Deployment
One of the best practices recommended by Microsoft is to limit the number of software updates to 1000 for each software update deployment. When you create an automatic deployment rule or manually deploy software updates, do not select more than 1000 updates to deploy. This will prevent the deployment from becoming too large and overwhelming the systems that are receiving the updates.
Create a New Software Update Group for Every Deployment
Another best practice is to create a new software update group each time an automatic deployment rule runs for “Patch Tuesday” or for general deployment. There is a limit of 1000 software updates for a software update deployment. When you create an automatic deployment rule, you can specify whether to use an existing update group or create a new update group each time the rule runs. If you specify criteria in an automatic deployment rule that results in multiple software updates and the rule runs on a recurring schedule, specify to create a new software update group each time the rule runs. This will prevent the deployment from surpassing the limit of 1000 software updates per deployment.
Use an Existing Software Update Group for Endpoint Protection Definition Updates
When you use an automatic deployment rule to deploy Endpoint Protection definition updates on a frequent basis, it is recommended to always use an existing software update group. Otherwise, potentially hundreds of software update groups will be created over time. Typically, definition update publishers will set definition updates to expire when they are superseded by four newer updates. Therefore, the software update group that is created by the automatic deployment rule will never contain more than four definition updates for the publisher: one active and three superseded.
Test updates before deploying them
It’s always a good idea to test updates in a non-production environment before deploying them in a production environment. This can help identify any issues or conflicts that may arise during the deployment process.
Use maintenance windows
Maintenance windows can be used to specify a period of time during which updates can be installed on client machines. This can help prevent updates from being installed during critical business hours or when users are actively working on their computers.
Monitor deployment status
It’s important to monitor the deployment status of updates to ensure that they are being installed successfully. SCCM provides various reports that can be used to monitor deployment status.
Keep SCCM up-to-date
It’s important to keep SCCM up-to-date with the latest updates and hotfixes. This can help ensure that SCCM is functioning properly and can help prevent any issues or bugs from affecting the update deployment process.
SCCM Update Deployment FAQs
| Question |
Answer |
What is SCCM?
|
SCCM stands for System Center Configuration Manager. It is a software management tool that allows organizations to manage and deploy software, updates, and patches across multiple devices and systems. |
What are some best practices for deploying updates with SCCM?
|
Some best practices for deploying updates with SCCM include scheduling updates during non-business hours, testing updates on a small group of devices before deploying to the entire organization, and creating a rollback plan in case of issues. It’s also important to regularly monitor the deployment process and report any issues or errors. |
How should updates be prioritized for deployment?
|
Updates should be prioritized based on their criticality and potential impact on the organization. Security updates should always be prioritized, followed by critical updates and then important updates. Updates that are not critical or important can be deferred or postponed. |
How often should updates be deployed?
|
The frequency of updates deployment can vary depending on the organization’s needs and policies. However, it’s generally recommended to deploy updates at least once a month to ensure that systems are protected against known vulnerabilities and threats. |
How can SCCM help with update deployment?
|
SCCM provides a centralized platform for managing and deploying updates across multiple devices and systems. It allows administrators to automate the update deployment process, monitor the deployment status, and report any issues or errors. SCCM can also help ensure that updates are deployed in a consistent and standardized manner, reducing the risk of errors and inconsistencies. |
Should you have a Patching Process / Schedule?
|
Yes, a patching process will schedule when you regularly deploy your updates. It helps monitor and track when patches should be deployed to which environment. |
What should be included in a rollback plan?
|
A rollback plan should include steps for undoing the update deployment, as well as a plan for communicating with end-users and stakeholders. It should also identify any potential risks or challenges associated with rolling back updates, and outline strategies for mitigating those risks.
You can also use SnaPatch, which automates a snapshot of your servers prior to patch deployment. This will allow you to easily roll back should a patch cause an issue to your sever fleet. |
How can SCCM help with update reporting?
|
SCCM provides a variety of reporting tools that allow administrators to monitor the status of update deployments, identify any issues or errors, and report on compliance with organizational policies and regulatory requirements. These reports can help ensure that systems are up-to-date and secure, and can also provide valuable insights into the overall health and performance of the IT environment. |
SCCM Update Deployment Final Thoughts
What is SCCM update deployment?
SCCM (System Center Configuration Manager) is a software management tool used by IT administrators to deploy updates to client machines. SCCM update deployment involves deploying software updates to client machines in a controlled and efficient manner.
Why is SCCM update deployment important?
SCCM update deployment is important because it helps ensure that client machines are up-to-date with the latest security patches and software updates. This can help prevent security vulnerabilities and improve the overall performance and stability of client machines.
What are some best practices for SCCM update deployment?
Some best practices for SCCM update deployment include limiting the number of software updates to 1000 per deployment, creating a new software update group for each automatic deployment rule, using an existing software update group for Endpoint Protection definition updates, testing updates before deployment, using maintenance windows, monitoring deployment status, and keeping SCCM up-to-date with the latest updates and hotfixes.
How do I monitor the deployment status of updates in SCCM?
SCCM provides various reports that can be used to monitor the deployment status of updates. These reports can be accessed from the SCCM console and can provide information on the success or failure of update deployments.
How often should I deploy updates in SCCM?
The frequency of update deployments in SCCM can vary depending on the organization’s needs and policies. However, it is generally recommended to deploy updates on a regular basis, such as monthly or quarterly, to ensure that client machines are up-to-date with the latest security patches and software updates.




 Thats all there is to it. SnaPatch will now create a deployment of the Zero Day Exploit Patch within Microsoft SCCM and set the Maintenance Window. When the maintenance window is reached, SnaPatch will interact with your Vmware or HyperV hosts and start a snapshot of the servers you have selected. Once the snapshot is complete SnaPatch then contacts SCCM and allows SCCM to deploy the patch to those servers. You will also receive email notifications throughout the snapshot and deployment process.
Thats all there is to it. SnaPatch will now create a deployment of the Zero Day Exploit Patch within Microsoft SCCM and set the Maintenance Window. When the maintenance window is reached, SnaPatch will interact with your Vmware or HyperV hosts and start a snapshot of the servers you have selected. Once the snapshot is complete SnaPatch then contacts SCCM and allows SCCM to deploy the patch to those servers. You will also receive email notifications throughout the snapshot and deployment process.