MICROSOFT’S November 2016 PATCH RELEASES
MICROSOFT’S November 2016 PATCH RELEASES
Microsoft have released 14 new Patch Tuesday releases for deployment this month of November.
See how you can remove the risk of patch deployment by adding SnaPatch to your SCCM patching infrastructure?
MS16-129 – Critical
Cumulative Security Update for Microsoft Edge (3199057)
This security update resolves vulnerabilities in Microsoft Edge. The most severe of the vulnerabilities could allow remote code execution if a user views a specially crafted webpage using Microsoft Edge. An attacker who successfully exploited the vulnerabilities could gain the same user rights as the current user. Customers whose accounts are configured to have fewer user rights on the system could be less impacted than users with administrative user rights.
MS16-130 – Critical
Security Update for Microsoft Windows (3199172)
This security update resolves vulnerabilities in Microsoft Windows. The most severe of the vulnerabilities could allow remote code execution if a locally authenticated attacker runs a specially crafted application.
MS16-131 – Critical
Security Update for Microsoft Video Control (3199151)
This security update resolves a vulnerability in Microsoft Windows. The vulnerability could allow remote code execution when Microsoft Video Control fails to properly handle objects in memory. An attacker who successfully exploited the vulnerability could run arbitrary code in the context of the current user. However, an attacker must first convince a user to open either a specially crafted file or a program from either a webpage or an email message.
MS16-132 – Critical
Security Update for Microsoft Graphics Component (3199120)
This security update resolves vulnerabilities in Microsoft Windows. The most severe being of the vulnerabilities could allow a remote code execution vulnerability exists when the Windows Animation Manager improperly handles objects in memory if a user visits a malicious webpage. An attacker who successfully exploited the vulnerability could install programs; view, change, or delete data; or create new accounts with full user rights.
MS16-133 – Important
Security Update for Microsoft Office (3199168)
This security update resolves vulnerabilities in Microsoft Office. The most severe of the vulnerabilities could allow remote code execution if a user opens a specially crafted Microsoft Office file. An attacker who successfully exploited the vulnerabilities could run arbitrary code in the context of the current user. Customers whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights.
MS16-134 – Important
Security Update for Common Log File System Driver (3193706)
This security update resolves vulnerabilities in Microsoft Windows. The vulnerability could allow elevation of privilege when the Windows Common Log File System (CLFS) driver improperly handles objects in memory. In a local attack scenario, an attacker could exploit these vulnerabilities by running a specially crafted application to take complete control over the affected system. An attacker who successfully exploits this vulnerability could run processes in an elevated context.
MS16-135 – Important
Security Update for Windows Kernel-Mode Drivers (3199135)
This security update resolves vulnerabilities in Microsoft Windows. The most severe of the vulnerabilities could allow elevation of privilege if an attacker logs on to an affected system and runs a specially crafted application that could exploit the vulnerabilities and take control of an affected system.
MS16-136 – Important
Security Update for SQL Server (3199641)
This security update resolves vulnerabilities in Microsoft SQL Server. The most severe vulnerabilities could allow an attacker could to gain elevated privileges that could be used to view, change, or delete data; or create new accounts. The security update addresses these most severe vulnerabilities by correcting how SQL Server handles pointer casting.
MS16-137 – Important
Security Update for Windows Authentication Methods (3199173)
This security update resolves vulnerabilities in Microsoft Windows. The more severe of the vulnerabilities could allow elevation of privilege. To exploit this vulnerability, the attacker would first need to authenticate to the target, domain-joined system using valid user credentials. An attacker who successfully exploited this vulnerability could elevate their permissions from unprivileged user account to administrator. The attacker could then install programs; view, change or delete data; or create new accounts. The attacker could subsequently attempt to elevate by locally executing a specially crafted application designed to manipulate NTLM password change requests.
MS16-138 – Important
Security Update to Microsoft Virtual Hard Disk Driver (3199647)
This security update resolves vulnerabilities in Microsoft Windows. The Windows Virtual Hard Disk Driver improperly handles user access to certain files. An attacker could manipulate files in locations not intended to be available to the user by exploiting this vulnerability.
MS16-139 – Important
Security Update for Windows Kernel (3199720)
This security update resolves a vulnerability in Microsoft Windows. The vulnerability could allow elevation of privilege if an attacker runs a specially crafted application to access sensitive information. A locally authenticated attacker could attempt to exploit this vulnerability by running a specially crafted application. An attacker can gain access to information not intended to be available to the user by using this method.
MS16-140 – Important
Security Update for Boot Manager (3193479)
This security update resolves a vulnerability in Microsoft Windows. The vulnerability could allow security feature bypass if a physically-present attacker installs an affected boot policy.
MS16-141 – Critical
Security Update for Adobe Flash Player (3202790)
This security update resolves vulnerabilities in Adobe Flash Player when installed on all supported editions of Windows 8.1, Windows Server 2012, Windows Server 2012 R2, Windows RT 8.1, Windows 10, and Windows Server 2016.
MS16-142 – Critical
Cumulative Security Update for Internet Explorer (3198467)
This security update resolves vulnerabilities in Internet Explorer. The most severe of the vulnerabilities could allow remote code execution if a user views a specially crafted webpage using Internet Explorer. An attacker who successfully exploited the vulnerabilities could gain the same user rights as the current user. If the current user is logged on with administrative user rights, an attacker could take control of an affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
Now that you have made it this far, a quick shameless plug for our software portfolio. 🙂
SnaPatch – Patch Management Addon for Microsoft’s SCCM.
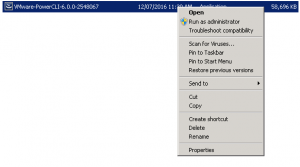
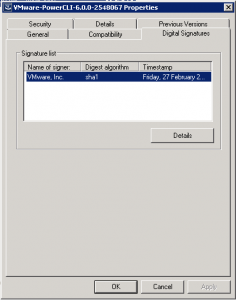
SnapShot Master – Take control of your virtual machine snapshots, works with both Hyper-V and Vmware.
Azure Virtual Machine Scheduler – Save money and schedule the shutdown and power on of your virtual machines within Microsoft’s Azure Cloud.
Azure Virtual Machine Deployer – Deploy VMs to Microsoft’s Azure cloud easily, without the need for powershell.