Deploying a Zero Day Exploit Fix with Microsoft SCCM 2012
Zero Day exploits are vulnerabilities that are found and can be used by hackers to exploit and use for malicious or personal intent. These exploits have been known to affect both software and hardware, causing issues to programs, data, computers, and networks. Once a patch or fix is released by the vendor, the issue is no longer known as a Zero Day vulnerability. In this article, we will discuss how to remediate Zero Day attacks and how to deploy a Zero Day exploit fix using Microsoft SCCM
Remediating Zero Day Attacks
Unfortunately, there isn’t much that can be done until a fix or update is released that patches the security hole. Once a patch is released, it is best to deploy and apply the patch as soon as possible. To reduce the risk of unknown vulnerabilities, it is good practice to keep your hardware and software up to date. This will remove any previously found vulnerabilities from your environment as patches are applied. Having a patching process in place and suitable infrastructure to do so (e.g., Microsoft SCCM and SnaPatch) where you can deploy updates easily and often are also good practices.
Deploying a Zero Day Exploit Patch Using SCCM
Unfortunately, there isn’t much that can be done until a fix or update is released that patches the security hole. Once a patch is released, it is best to deploy and apply the patch as soon as possible. To reduce the risk of unknown vulnerabilities, it is good practice to keep your hardware and software up to date. This will remove any previously found vulnerabilities from your environment as patches are applied. Having a patching process in place and suitable infrastructure to do so (e.g., Microsoft SCCM and SnaPatch) where you can deploy updates easily and often are also good practices.
Zero Day Exploit Overview
So what exactly is a Zero Day Exploit you ask? To be exact, a Zero Day Exploit is a vulnerability that is found that a possible Hacker can use to exploit and use for malicious or personal intent. The Vendor (software or hardware) has Zero Days to plan, mitigate and fix the issue so that there is no further exploitation of the vulnerability. The exploits have been known to be for either software (Operating Systems and Software) and hardware. They have been known to cause issues to programs, data, computers and to the network.
Zero Day Attack Timeline
In the case of a breach being found in some software, a Zero Day Exploit normally follows this;
- A hacker finds a vulnerability with a product (software/hardware).
- The hacker writes an exploit and uses it either to be malicious or financial gain.
- Exploit is detected either by Users, Security Companies or the Vendor themselves.
- The Vendor studies the new exploit and develops a fix.
- The Vendor releases a new patch to fix the exploit
- Users install the Patch or Virus Definition update.
The biggest issue with a Zero Day Exploit is that they are generally unknown until they have been used to breach systems, leaving everyone vulnerable until the Vendor releases security advice on how to remediate the issue or a patch or update. This could be days, weeks, months or even years before the Vendor learns of the vulnerability. Once a Patch or Fix has been released by the Vendor, then the issue is no longer known as a Zero Day Vulnerability.
How to remediate Zero Day Attacks
Unfortunately there isnt much that can be done until there is a fix or update released that patches the security hole. Once a patch is released it is best to deploy and apply the patch as soon as is possible.
To also reduce the risk, it is good practice which will aid you in mitigation of vulnerabilities that are unknown to yourself if you keep your hardware and software patched up to date. This will remove from your environment any previously found vulnerabilities as patches are applied. Having a Patching Process in place and suitable infrastructure to do so (ie Microsoft SCCM and SnaPatch for instance) where you can deploy updates easily and often are also good practice.
Using SCCM to deploy a Zero Day Exploit Patch
If you are using Microsofts SCCM 2012, you can easily deploy an update that addresses a Zero Day Vulnerability by following these steps;
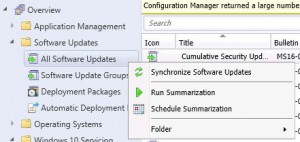
- Log on to your SCCM console, then go to Software Library, then expand Software Updates and highlight All Software Upates. Now Right Click and choose Synchronise Software Updates. This will synchronise your SCCM server with your WSUS updates server. Allow a few minutes for the new updates to populate the view. You can check the Wsyncmgr.log to view the update synchronisation.

- If you know the Bulletin ID number (the update number released by Microsoft in the format MSXX-XXX. In this example I am choosing MS16-082), you can now search for this within the console.

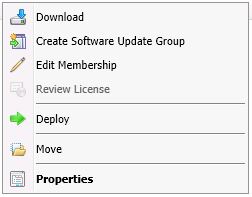
- Make sure that the update has downloaded and if not, right click the update and choose Download. You will obviously need to give the update sometime to download in to your environment and be ready for deployment. Click this link to see how to manually download updates if you dont know how.

- When the update is downloaded and ready for deployment, you are now ready to deploy the Update. (If you are using SnaPatch to deploy the updates, go straight to the SnaPatch Section below.)
Right Click the update (or updates) and choose Deploy.
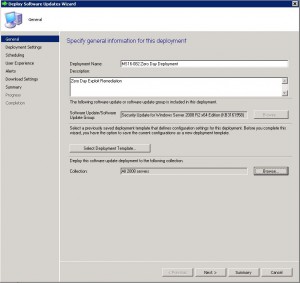
Enter in a Deployment Name, a Description, and choose the collection you wish the Zero Day exploit to deploy to. Once you have chosen the correct settings, click on Next.
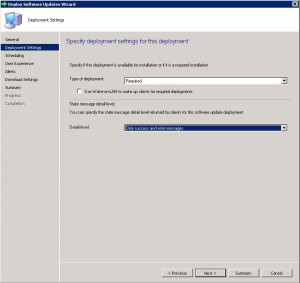
- On the Deployment Tab, leave the type of deployment as Required and choose the level of detail you want then click on Next.

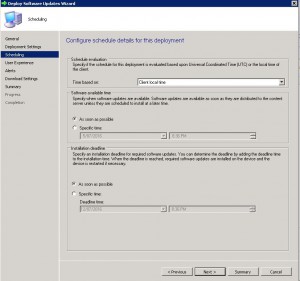
- Now to schedule when you want the update to deploy. As this is a Zero Day Exploit that you want patched quickly, schedule the patch to be available As Soon As Possible for both the Software Available Time and Installation Deadline. Please note, that more often than not, the installation of an update will cause systems to restart. Please make sure you have informed the appropriate people and that you have approval for deployment. Nothing worse than deploying an update and having to answer to Management as you caused unwarranted system outages.

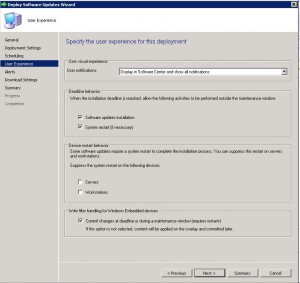
- The User Experience Tab is where you set how the deployment will interact with Users. You can set if the users are notified within the Software Centre that an update is available for installation, when the deployment deadline is reached whether the update can install and restart the system outside a maintenance window, and finally whether you wish to suppress a system restart. As this is an urgent deployment, I have chosen to allow installation and restart to be allowed outside any maintenance windows. Choose the settings you require and click on Next.

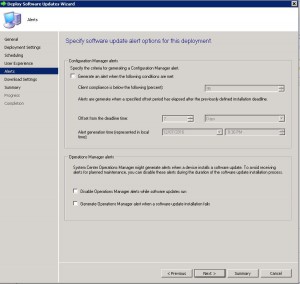
- If you have System Centre Operations Manager (Microsoft SCOM) in your environment you can choose to generate an alert with criteria you specify. In this example we are not going to specify any settings. Click on Next when you have made your selections.

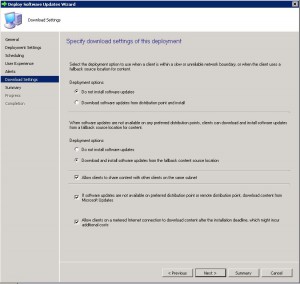
- The Download Settings tab allows you to choose client download settings. If a client is on a slow or unreliable network boundary you can choose if they dont install the update or from another distribution point. Allowing clients to share content between themselves is a great feature of SCCM as it will stop other client machines downloading the same updates and possibly flooding a network link. The clients will all share the update between themselves if they are on the same subnet. Also if they cannot download the update from a SCCM distribution point, allowing them to download from Microsoft Update is available as well.
Click on Next when ready to.
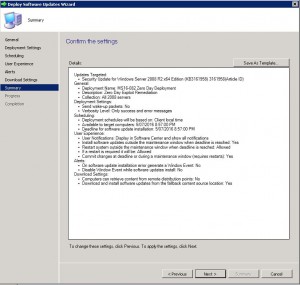
- Now you can review all the settings on the Summary Tab. Confirm you are happy with all the settings and then click Next.

- The progress of the deployment will now be shown.

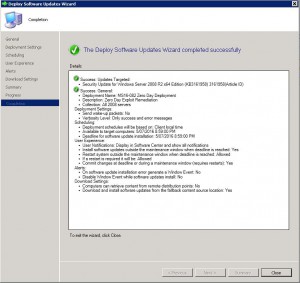
- Your Zero Day Exploit deployment should now be ready to be deployed to your SCCM clients as per the settings you have set.

Using SnaPatch for Zero Day Exploit Deployment
If you are using SnaPatch to aid you with the deployment of Windows Updates with Microsoft’s SCCM, you can follow on from Steps 1 to 4 from above.
- Open the SnaPatch console and choose the SnaPatch Icon to start the snapshot and patch deployment process.

- Now you are presented with all the SCCM Collections and Systems available to deploy the Zero Day Exploit to. Choose the systems you want to receive the patch and click on Add.

If the machines are virtual (either a VMWare or HyperV virtual machine) you can choose whether to take a snapshot of the servers prior to deployment of the zero day patch. Should the servers not have a successfully snapshot completed, then they will not receive the update deployment. The snapshot of the virtual machines gives you a quick rollback position should the update cause an issue in your environment.
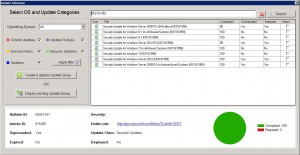
When you have chosen all the machines you wish and if you would like a snapshot, click on the green arrow to continue. - The next window in the SnaPatch process, is to chose the update you wish to deploy. As this is a Zero Day patch and we know the Microsoft article number (which in this example is MS16-082), type in the KB or MS article number and choose search.
Select the update, confirm that it has been downloaded (as per step 3 above) and now choose if you want the update to deploy to an existing Update Group or to create a new one.
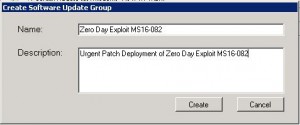
- As this is an urgent deployment, I am choosing Create & Deploy Update Group. Give the Software Update Group a Name and Description and click Create.

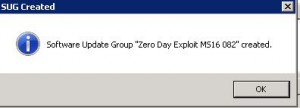
- Confirmation that the Software Update Group has been created. Click OK.

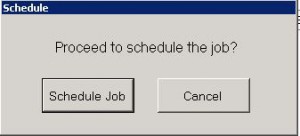
- Next we have to schedule deployment. Click Schedule Job.

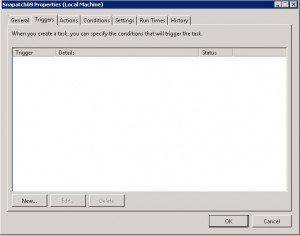
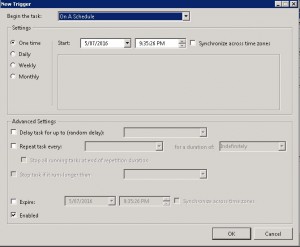
- Now on the scheduling window, click on New.

- Choose an appropriate schedule when you would like the deployment to happen. This will set up the update deployment for the time you specify. Click OK when you are ready to proceed, then close the scheduling Window.

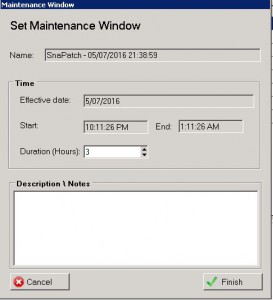
- On the Maintenance Window choose the duration you want the snapshots to be performed and the updates to be installed during. Click on Finish when complete.
 Thats all there is to it. SnaPatch will now create a deployment of the Zero Day Exploit Patch within Microsoft SCCM and set the Maintenance Window. When the maintenance window is reached, SnaPatch will interact with your Vmware or HyperV hosts and start a snapshot of the servers you have selected. Once the snapshot is complete SnaPatch then contacts SCCM and allows SCCM to deploy the patch to those servers. You will also receive email notifications throughout the snapshot and deployment process.
Thats all there is to it. SnaPatch will now create a deployment of the Zero Day Exploit Patch within Microsoft SCCM and set the Maintenance Window. When the maintenance window is reached, SnaPatch will interact with your Vmware or HyperV hosts and start a snapshot of the servers you have selected. Once the snapshot is complete SnaPatch then contacts SCCM and allows SCCM to deploy the patch to those servers. You will also receive email notifications throughout the snapshot and deployment process.
Click for further information on SnaPatch Patch Management.
Zero Day exploits can cause serious issues to programs, data, computers, and networks. It is essential to deploy patches and fixes as soon as possible to reduce the risk of exploitation. Using Microsoft SCCM 2012 to deploy a Zero Day exploit fix is an easy process that can be completed by following the steps outlined above. Keeping your hardware and software up to date and having a patching process in place are good practices to mitigate the risk of unknown vulnerabilities.





 T
T